iPhone users have been warned of a new type of phishing scam that tricks you into giving away your Apple ID.
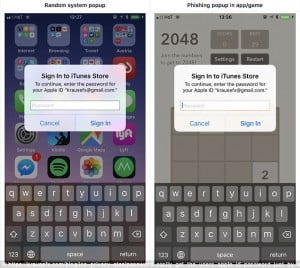
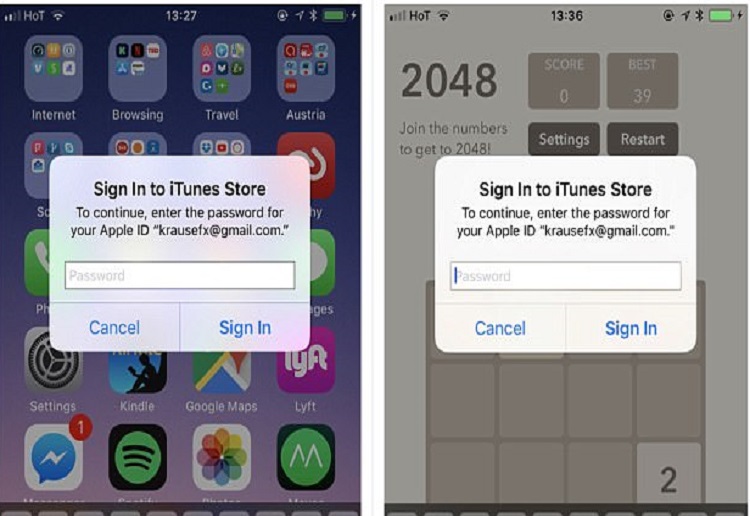
Malicious iOS apps can easily create fake login pop-ups that look exactly like the ones used by Apple, an expert cautioned.
The login boxes usually appear when you try to install or update an app, and ask you to enter your Apple ID password before you can continue.
If you input your password into one of the fake boxes, the attacker could steal it and use it to access your credit card information.
App developer Felix Krause, based in Vienna, Austria, published a proof-of-concept on his blog on Tuesday that showed how easy it is to copy Apple’s ‘Sign In to iTunes Store’ prompt to take a user’s password.
Mr Krause said malicious developers can turn on alerts inside their apps that look almost identical to Apple’s pop-ups using a simple bit of code.
‘Users are trained to just enter their Apple ID password whenever iOS prompts you to do so,’ Mr Krause wrote in his post.
‘However, those popups are not only shown on the lock screen, and the home screen, but also inside random apps, e.g. when they want to access iCloud, GameCenter or In-App-Purchases. This could easily be abused by any app.’
Hackers who access your Apple ID password could make fraudulent purchases and potentially steal your payment information.
If you use your Apple ID password elsewhere, like your online banking service, cyber criminals could use it to crack your accounts.
How to protect yourself
You can protect yourself from the fake pop-up scam by never inputting passwords into an Apple pop-up.
Instead, Mr Krause said, you should go into your iPhone’s settings menu and enter it there to confirm it’s a real request from Apple.
You can also click the home button whenever a pop-up is shown.
Mr Krause said this will close the app if it is a phishing scam, but the pop-up will remain if it is a legitimate Apple ID request.
You should also always have two-factor authentication activated on your Apple account for an extra layer of security.
Share your comments below
We may get commissions for purchases made using links in this post. Learn more.


















8:17 pm
2:40 pm
2:14 pm
2:34 pm
1:37 pm
9:19 am
8:01 am
7:49 am
7:03 am
-

-
-
-
mom93821 replied
- 14 Oct 2017 , 7:53 am
Reply6:28 am
9:55 pm
9:25 pm
8:03 pm
5:31 pm
5:02 pm
- 1
- 2
- »
Post a comment